Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
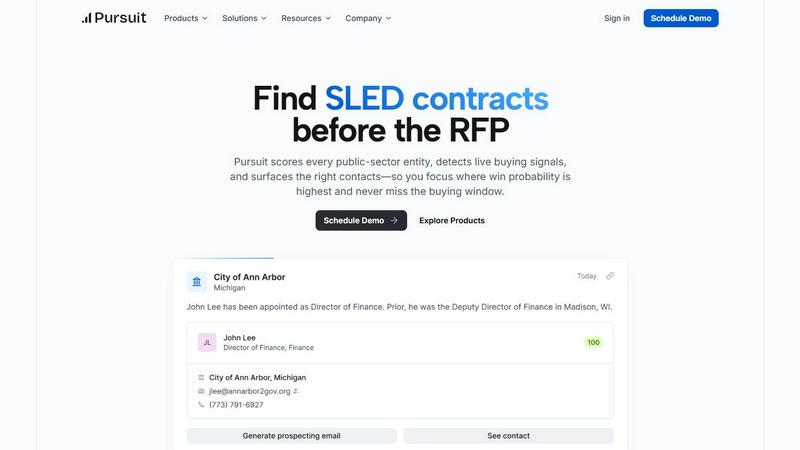
Pursuit
Pursuit uses AI to reveal public sector deals long before the RFP is announced.
Last updated: February 28, 2026
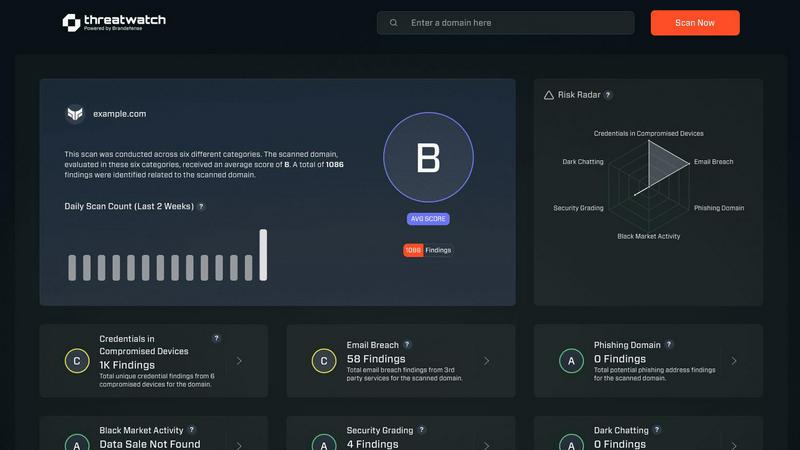
Threat Watch
Instantly assess your cybersecurity health with actionable insights across critical risk categories.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
AI-Powered Buying Signal Detection
Pursuit's AI engine continuously scans and analyzes millions of data points from across the SLED landscape, including budget approvals, leadership changes, contract expirations, and committee meetings. It distills this unstructured information into clear, scored buying signals, alerting users to genuine in-market intent long before an RFP is published. This transforms hidden intelligence into a competitive advantage, ensuring teams never miss a critical budget cycle or procurement window.
Entity Scoring & Prioritization
The platform assigns a dynamic score to every public-sector entity, evaluating its likelihood to purchase based on live signals, historical procurement data, and budgetary health. This allows sales and marketing teams to move beyond guesswork and manually built lists, instead focusing their efforts with precision on the accounts with the highest propensity to buy, thereby maximizing efficiency and pipeline quality.
Native CRM & MarTech Integrations
Pursuit is built for seamless operation within existing tech stacks. It offers bi-directional synchronization with major CRMs like Salesforce and HubSpot, ensuring enriched account data, contacts, and buying signals flow automatically without manual entry. Marketing teams can also push targeted audiences directly to platforms like LinkedIn Ads, Marketo, or HubSpot to run signal-informed ABM campaigns.
Chrome Extension for Instant Intelligence
This tool empowers customer-facing teams with real-time context during their workflow. While browsing a government entity's website or preparing for a call, the extension surfaces key Pursuit intelligence directly in the browser, including incumbent vendors, contract values, recent buying signals, and organizational charts, enabling more informed and impactful conversations.
Threat Watch
Unified Threat Intelligence Dashboard
This central command center synthesizes data from across the clear, deep, and dark web into a single pane of glass. It transforms overwhelming, disparate data streams into a coherent visual narrative of your organization's security posture, enabling rapid comprehension and decision-making without the need to juggle multiple tools or reports.
Automated Cyber Health Assessment
Threat Watch automates the continuous evaluation of critical security categories, providing a fast and comprehensive scan of your digital footprint. This feature delivers an immediate diagnostic of key risk areas, including compromised credentials, breached accounts, and vulnerable devices, establishing a clear baseline for your cybersecurity health.
Proactive Dark Web Monitoring
The platform actively patrols dark web marketplaces, forums, and private channels where stolen data is traded. This proactive surveillance is crucial for early detection of compromised employee credentials, leaked intellectual property, or planned attacks against your organization, offering a vital early warning system.
Prioritized Risk Insights and Alerts
Beyond simple detection, Threat Watch employs intelligent analytics to triage and prioritize threats based on context and potential impact. This means security teams are guided directly to the most critical issues first, such as active credential misuse or high-severity vulnerabilities, optimizing response efforts and resource allocation.
Use Cases
Pursuit
Proactive Pipeline Generation for BDRs/SDRs
Business Development Representatives stop cold calling blindly. Pursuit provides daily, prioritized call and outreach lists based on verified buying signals within their territory, such as a new budget approval or a contract nearing expiration. This shifts outreach from speculative to relevant, dramatically increasing connection and qualification rates.
Strategic Account Planning for Sales Leaders
Sales executives and managers gain a macro view of their team's entire SLED footprint. They can analyze territory coverage, identify strategic gaps, and forecast more accurately using real buying indicators rather than intuition. This visibility allows for better resource allocation and coaching, driving overall team performance and pipeline growth.
Signal-Driven ABM for Marketing
Marketing teams can construct highly targeted account-based marketing campaigns anchored in real-time intelligence. By targeting accounts with specific, active signals—like a new technology initiative in a city's approved budget—campaigns achieve greater relevance and impact, leading to higher engagement and conversion rates throughout the buyer's journey.
Renewal & Churn Risk Management for Customer Success
Customer Success managers configure alerts for key renewal windows (e.g., 90-180 days prior) and receive notifications of potential churn risks, such as budget cuts, leadership changes, or competitor RFPs targeting their accounts. This early warning system allows for proactive retention strategies, securing renewals faster and protecting revenue.
Threat Watch
Proactive Breach Response and Mitigation
Security teams use Threat Watch to shift from reacting to breach notifications to proactively discovering them. By identifying compromised employee credentials or corporate data on the dark web before they are actively exploited, organizations can force password resets and secure accounts, effectively neutralizing a threat before an attack begins.
Third-Party and Supply Chain Risk Management
Risk professionals leverage the platform to extend visibility beyond their own perimeter. By monitoring for breaches and exposures associated with vendors, partners, and suppliers, organizations can assess third-party risk and initiate crucial conversations to strengthen the security of their entire ecosystem.
Executive and Board-Level Risk Reporting
Business leaders utilize the clear, consolidated dashboard to gain an accurate, real-time understanding of organizational cyber risk. The visual reports and prioritized metrics translate technical data into strategic business intelligence, supporting informed decision-making and resource justification for security investments.
IT Asset and Vulnerability Management
IT and security operations teams integrate Threat Watch findings with their asset inventories. The platform helps identify unknown or unmanaged devices exposed on the internet, and correlates them with known vulnerabilities, ensuring that patching and remediation efforts are focused on the assets most likely to be targeted.
Overview
About Pursuit
Pursuit is a Pre-RFP Intelligence Platform engineered to transform how businesses sell to the State, Local, and Education (SLED) government market. It directly confronts the immense complexity of public-sector sales, where over 110,000 unique entities operate on long budget cycles and opaque procurement processes. The platform's core mission is to shift sales teams from a reactive posture—scrambling to respond to public RFPs—to a proactive strategy, identifying and engaging opportunities 6-18 months before a formal request ever hits the street. By leveraging advanced AI to continuously monitor and score entities for live buying signals buried in budget documents, council meetings, and contract postings, Pursuit provides unparalleled visibility. This enables government contractors and B2B companies to focus resources where the probability of winning is highest, build relevance with key stakeholders early, and ultimately show up as the incumbent solution rather than an outsider. It's more than a database; it's a shared system of intelligence that aligns marketing, sales development, account executives, and customer success around actionable signals, driving measurable outcomes like pipeline growth, improved win rates, and faster renewals.
About Threat Watch
Threat Watch is not merely a monitoring tool; it is a strategic cybersecurity intelligence platform that fundamentally shifts how organizations perceive and manage digital risk. It acts as a centralized diagnostic hub, providing a real-time, holistic view of an organization's cyber health by continuously scanning and correlating data across the clear, deep, and dark web. Designed for IT security teams, risk management professionals, and forward-thinking business leaders, its core mission is to dismantle reactive security postures. By consolidating fragmented threat data—from exposed credentials and breached accounts to vulnerable devices and phishing campaigns—into a single, intuitive dashboard, Threat Watch delivers prioritized, actionable insights. This empowers organizations to move with speed and precision, closing the window of opportunity for attackers by mitigating critical risks before they escalate, thereby building a more resilient and intelligence-driven security foundation.
Frequently Asked Questions
Pursuit FAQ
What types of buying signals does Pursuit identify?
Pursuit identifies a wide range of actionable signals indicative of future procurement. This includes budget approvals for specific projects, contract expiration dates, leadership changes in relevant departments, mentions of initiatives in council meeting minutes, pre-RFP market research solicitations, and the posting of past RFPs from similar entities. The AI contextualizes these signals to score an entity's buying intent.
How does Pursuit ensure data accuracy for 110,000+ entities?
The platform employs a multi-faceted approach to ensure high data fidelity. It combines automated, continuous data ingestion from thousands of primary sources (government websites, portals) with AI-driven parsing and enrichment. This process is supplemented by ongoing data hygiene practices and validation, aiming for a documented 94% accuracy rate in account and contact information.
Can Pursuit integrate with our existing sales and marketing tools?
Yes, native integration is a core feature. Pursuit offers out-of-the-box, bi-directional sync with major CRM platforms like Salesforce and HubSpot, ensuring signal and account data flows seamlessly into your system of record. For marketing teams, integrations allow for the export of targeted account lists directly into advertising platforms (LinkedIn Ads) and marketing automation tools (Marketo, HubSpot).
Is Pursuit suitable for companies new to selling to the SLED market?
Absolutely. While invaluable for experienced government contractors, Pursuit is particularly powerful for companies expanding into the SLED sector. It dramatically reduces the steep learning curve by providing clarity on procurement processes, identifying the right entities to target, and revealing the critical timing of budget cycles, effectively de-risking market entry and accelerating time-to-revenue.
Threat Watch FAQ
What does Threat Watch actually scan and monitor?
Threat Watch conducts a comprehensive scan across multiple layers of the internet. This includes the clear web (publicly accessible information), the deep web (unindexed databases), and the dark web (obfuscated networks). It specifically hunts for compromised employee credentials, breached account details, phishing sites targeting your domain, vulnerable devices, and mentions of your organization's assets in criminal forums.
How is Threat Watch different from a traditional vulnerability scanner?
While vulnerability scanners focus on identifying technical weaknesses within your known IT infrastructure, Threat Watch operates from an external, intelligence-led perspective. It discovers risks you may not know exist—like stolen credentials on the dark web or a shadow IT server exposed online—providing context about how attackers might actually target you, not just what flaws are present.
Who inside an organization typically uses this platform?
Threat Watch serves multiple roles. Security analysts and SOC teams use it for daily threat hunting and incident response. IT managers use it to discover unmanaged assets. Risk and compliance officers use it for reporting and third-party assessment. Finally, CISOs and business executives use the high-level dashboard to oversee the organization's cyber risk posture.
How quickly can I see results after starting a scan?
The platform is designed for rapid insight. Upon initiating a free scan, Threat Watch immediately begins assessing your provided domains and key terms against its intelligence databases. You can receive initial findings on critical categories like compromised credentials and breached accounts within minutes, providing immediate value and a starting point for deeper investigation.
Alternatives
Pursuit Alternatives
Pursuit is an AI-driven business intelligence platform specifically designed to streamline sales in the public sector. It helps government contractors and businesses identify, score, and engage with state, local, and educational buying opportunities by surfacing live buying signals and actionable insights. Users often explore alternatives for various reasons, including budget constraints, the need for different feature sets, or a preference for a platform that integrates with a broader range of CRM systems. Some may seek solutions with a different geographic focus or require more general-purpose sales intelligence tools not solely dedicated to the public sector. When evaluating an alternative, key considerations should include the depth and accuracy of data for your target market, the platform's ability to provide real-time alerts on relevant opportunities, and the ease of integration into your existing sales workflow. The quality of contact information and the sophistication of predictive analytics are also critical factors to assess.
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence platform that falls under the broader category of business intelligence tools, specifically focused on providing a real-time, actionable view of an organization's digital security posture. It consolidates threat data to offer proactive insights into risks like compromised credentials and vulnerable assets. Users often explore alternatives for various practical reasons. These can include budget constraints, the need for a different feature set, integration requirements with existing security stacks, or a preference for a platform with a different operational focus, such as deeper compliance reporting or more specialized threat hunting capabilities. When evaluating other options, key considerations should align with your primary needs. Look for the scope of monitoring (clear, deep, and dark web coverage), the quality and speed of actionable alerts, ease of integration, and the platform's ability to prioritize risks effectively to reduce your overall attack surface and improve cyber resilience.
