Perkoon vs Phishly
Side-by-side comparison to help you choose the right AI tool.
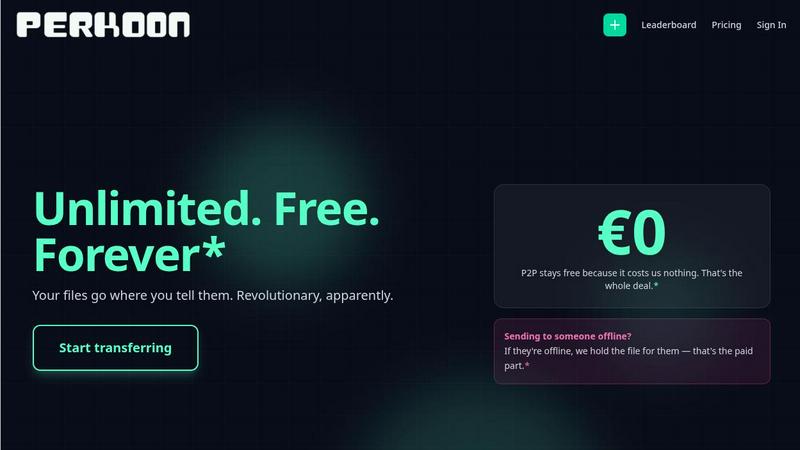
Perkoon offers free, unlimited peer-to-peer file transfers with no signup required.
Last updated: March 4, 2026
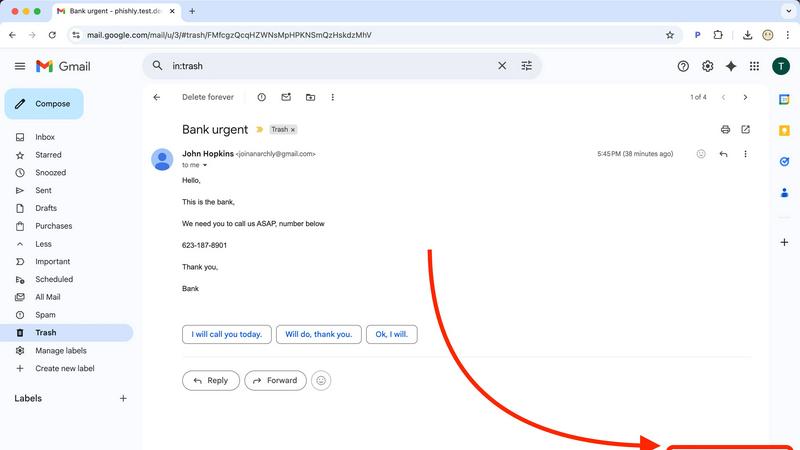
Phishly
Phishly uses AI to instantly detect phishing emails in your Gmail inbox.
Visual Comparison
Perkoon
Phishly
Feature Comparison
Perkoon
Truly Free Peer-to-Peer (P2P) Transfers
This is Perkoon's cornerstone feature. It enables direct, browser-to-browser file transfers with no intermediary server. This architecture means there are absolutely no file size limits, no mandatory account creation, and complete privacy as Perkoon cannot access the data stream. The service is free in perpetuity because this direct transfer model incurs negligible infrastructure costs for the company, a cost-saving passed directly to the user.
Honest Encrypted Cloud Storage
For when the recipient is offline, Perkoon provides a paid cloud storage solution. The service is upfront about this being a paid feature, as it honestly covers the cost of running and maintaining secure servers. Files stored in the cloud are encrypted, providing a secure holding zone. This transparent "pay for what costs us" model contrasts sharply with services that offer "free" tiers subsidized by data mining.
Native AI & Automation Integration
Perkoon is built for the future of work. It features window.__perkoon, a dedicated JavaScript object that allows AI agents and automation scripts to interact with the service programmatically without resorting to unreliable screen-scraping techniques. This native design makes it a robust tool for developers and users who incorporate AI assistants into their workflows for seamless file transfer automation.
Simple CLI and Referral Ecosystem
Beyond the web interface, Perkoon offers a Command Line Interface tool for power users who prefer terminal-based operations. Additionally, it features a community-driven referral program. Users can share a unique link; when new users sign up and perform transfers, both the referrer and referee earn bonus cloud storage, creating a sustainable growth model that rewards the community.
Phishly
AI-Powered Phishing Detection Engine
At the heart of Phishly is a sophisticated artificial intelligence system trained to identify a wide spectrum of phishing indicators. This goes beyond simple link checking. The AI scrutinizes the email's content for urgent or threatening language designed to provoke panic, analyzes the sender's address for subtle spoofing attempts (like replacing an 'm' with 'rn'), and evaluates the overall structure for social engineering tactics. This multi-layered analysis ensures a comprehensive threat assessment that adapts to evolving phishing strategies, providing a depth of scrutiny that manual inspection would likely miss.
Seamless Gmail Integration via Chrome Extension
Phishly eliminates friction by embedding its protective capabilities directly into your most-used workflow. The Chrome extension for Gmail adds a discreet "Scan with Phishly" button to your email interface. With a single click on any open email, the analysis begins instantly. This seamless integration means you don't have to copy, paste, or navigate away from your inbox, allowing for rapid decision-making precisely when you encounter a dubious message, thereby maintaining your productivity and security posture simultaneously.
Clear, Actionable Risk Assessment & Explanations
Phishly understands that a simple "danger" alert can be as paralyzing as the phishing attempt itself. Instead, it provides a clear, tri-color risk rating: Safe, Medium Risk, or High Risk. Each rating is accompanied by a detailed, plain-language explanation of the findings. For instance, it might specify, "The sender's domain 'paypa1.com' is a common misspelling of 'paypal.com'," or "This email uses urgent language demanding immediate payment." This transparency educates the user, building their own phishing awareness over time while providing the immediate context needed to decide whether to delete, report, or proceed with caution.
Privacy-First Web Tool for Versatile Analysis
For emails outside of Gmail or for users who prefer not to use an extension, Phishly offers a versatile web-based tool. You can paste the headers and content of any suspicious email—whether from Outlook, a work server, or a forwarded message—into the website for an instant scan. This feature underscores Phishly's commitment to privacy; analysis is performed only on the content you explicitly provide, with no continuous monitoring or data harvesting. It's a powerful, on-demand tool that respects user autonomy and data boundaries.
Use Cases
Perkoon
Sending Large Media Files Freely
Videographers, photographers, and designers can send massive project files, raw footage, or high-resolution image sets without worrying about arbitrary caps, compression, or expensive subscription tiers. The unlimited P2P transfer is ideal for collaborative creative work where large data packets are the norm and budgets may be tight.
Secure and Private Document Sharing
Legal professionals, journalists, or anyone handling sensitive information can utilize the direct P2P transfer for confidential documents. Since the data never passes through a central server and Perkoon cannot see the content, it offers a higher degree of privacy for one-time secure document exchange compared to traditional cloud services.
Automated Workflow and AI Agent Tasks
Developers and tech-savvy users can integrate Perkoon into automated pipelines. An AI agent could be programmed to automatically back up generated reports via the CLI or use the native API to fetch and process files uploaded by a client, all without manual intervention, streamlining complex digital workflows.
Offline File Delivery via Cloud Link
When you need to send a file to a colleague or client who isn't currently available online, you can use Perkoon's encrypted cloud storage. You upload the file, and Perkoon holds it securely, generating a link you can send. The recipient can then download it at their convenience, solving the common problem of asynchronous file sharing.
Phishly
The Cautious Individual and Family User
For everyday internet users managing personal emails, online shopping accounts, and social media notifications, Phishly acts as a first line of defense. When a user receives an unexpected "bank alert" or a too-good-to-be-true offer, they can instantly scan it. This empowers individuals and families to protect their personal finances and identities from sophisticated scams that often bypass traditional spam filters, fostering safer digital habits for all ages without requiring technical expertise.
The Small Business Owner or Freelancer
Small businesses and freelancers are prime targets for phishing due to often-limited IT resources. A successful attack can mean financial loss or data breach. Phishly provides these professionals with an enterprise-grade security check at zero cost. Before clicking a link in an invoice from a new "vendor" or opening an attachment from a "client," they can verify its legitimacy in seconds, safeguarding their business operations, sensitive client data, and hard-earned revenue.
The Remote and Hybrid Workforce Employee
Employees working outside the traditional office firewall are particularly vulnerable. Phishly equips remote workers with a personal security assistant directly in their inbox. Whether assessing a link in a supposed HR update or a file shared via a collaborative platform, they can independently verify emails without always needing to escalate to an IT helpdesk. This reduces organizational risk and increases employee confidence and productivity in distributed work environments.
The IT Trainer and Security Awareness Advocate
For professionals responsible for security awareness training, Phishly serves as an excellent educational tool. Instead of theoretical examples, trainers can use real (or simulated) emails with the class, scanning them live to demonstrate the AI's findings. This hands-on approach makes the lessons on spoofed domains, psychological manipulation, and other tactics tangible and memorable, significantly improving the effectiveness of cybersecurity education programs.
Overview
About Perkoon
Perkoon is a paradigm shift in file transfer, rejecting the modern playbook of surveillance, artificial restrictions, and data monetization. It is a service built on a radical principle of honesty: moving files from one point to another should be simple, private, and fair. It serves a diverse audience, from individuals tired of mandatory accounts and hidden fees to developers and power users seeking automation-friendly tools. Its core value proposition is a two-tiered, transparent model. The flagship offering is a truly unlimited and free peer-to-peer (P2P) transfer service that operates directly between browsers when both parties are online, imposing no size limits and requiring no sign-up. This is free forever because the data never touches Perkoon's servers, costing them nothing. For asynchronous transfers, Perkoon offers encrypted, paid cloud storage, openly acknowledging this covers their server costs. Uniquely, Perkoon is natively designed for the age of automation, featuring built-in APIs for AI agents and a CLI tool, positioning itself as the straightforward, powerful, and privacy-respecting file transfer solution for both people and the machines that assist them.
About Phishly
In the digital age, where our inboxes serve as gateways to both opportunity and peril, discerning friend from foe in an email has become a critical daily skill. Phishly emerges as a vigilant, AI-powered sentinel designed to demystify this threat landscape. At its core, Phishly is an intuitive phishing detection platform that operates directly where you need it most: within your Gmail via a Chrome extension and on the web for broader analysis. Its primary mission is to provide instant, clear-eyed analysis of suspicious emails, transforming uncertainty into actionable insight. By simply opening an email in Gmail and clicking "Scan with Phishly" or pasting email content on their website, users receive an immediate risk assessment categorized as Safe, Medium Risk, or High Risk. This tool is meticulously crafted for individuals, remote workers, and small to medium-sized businesses who seek robust phishing protection without the overhead, complexity, or cost of enterprise-grade security suites. Its profound value proposition lies in its simplicity, speed, and unwavering commitment to privacy—it only analyzes emails you explicitly submit, ensuring your digital correspondence remains confidential. By translating complex threat indicators like domain spoofing, social engineering tactics, and malicious links into plain language, Phishly empowers everyone to navigate their inbox with confidence.
Frequently Asked Questions
Perkoon FAQ
How can P2P transfers be completely free?
P2P transfers are free because of the underlying technology. The files are streamed directly from the sender's browser to the recipient's browser without ever being stored on or routed through Perkoon's servers. This direct connection means Perkoon incurs virtually no bandwidth or storage costs for these transfers, allowing them to offer the service for free indefinitely.
What happens if the recipient is offline?
If the recipient is not online to receive a direct P2P transfer, Perkoon offers encrypted cloud storage as a solution. This is a paid feature. The sender can upload the file to Perkoon's secure servers, where it is held encrypted. A link is then provided that can be sent to the recipient for download at their convenience.
Can Perkoon see the files I send via P2P?
No, absolutely not. During a peer-to-peer transfer, the file data is encrypted and transmitted directly between the two users' web browsers using WebRTC data channels. Perkoon's servers only facilitate the initial connection ("signaling") but never have access to the actual file content, ensuring true privacy.
Is Perkoon compatible with AI agents and automation?
Yes, uniquely so. Perkoon is built with a native API for automation, exposed via window.__perkoon in the browser. This allows AI agents and scripts to interact with the service directly to initiate transfers or check statuses programmatically, eliminating the need for fragile and inefficient web scraping techniques.
Phishly FAQ
How does Phishly protect my privacy?
Phishly is built on a principle of explicit user consent and minimal data handling. The Chrome extension and web tool only analyze the specific email content you choose to submit for a scan. It does not continuously monitor your inbox, read your other emails, store your personal data, or track your browsing activity. Your scans are processed to provide the risk assessment and then discarded, ensuring your private communications remain just that—private.
Is Phishly really free to use?
Yes, based on the provided information, Phishly is currently free to use. This makes its advanced AI-powered phishing detection accessible to individuals, small businesses, and organizations of any size without a financial barrier. The company may offer the service for free to build a user base, gather anonymized threat data to improve its AI, or as part of a freemium model where advanced features could be introduced later, but the core scanning functionality is available at no cost.
What makes Phishly different from my email provider's spam filter?
Traditional spam filters operate automatically in the background, primarily filtering based on volume, known bad senders, and basic content rules. Phishly is a targeted, on-demand analysis tool. It uses advanced AI to deconstruct the specific content, context, and subtle deception techniques of an individual email that has already passed through the spam filter. It's designed for the sophisticated, targeted attacks (spear phishing) that often appear legitimate and require human-like scrutiny to detect.
Do I need technical knowledge to use Phishly?
Absolutely not. Phishly is designed for ease of use by anyone. The interface is straightforward: a single click in Gmail or a paste into the website. The results are presented in simple, clear language with a color-coded risk level (Safe, Medium, High) and bullet-point explanations of what triggered the alert. There is no configuration, complex settings, or cybersecurity jargon required, making powerful protection instantly accessible.
