AutoPhish vs Decode This Text
Side-by-side comparison to help you choose the right AI tool.
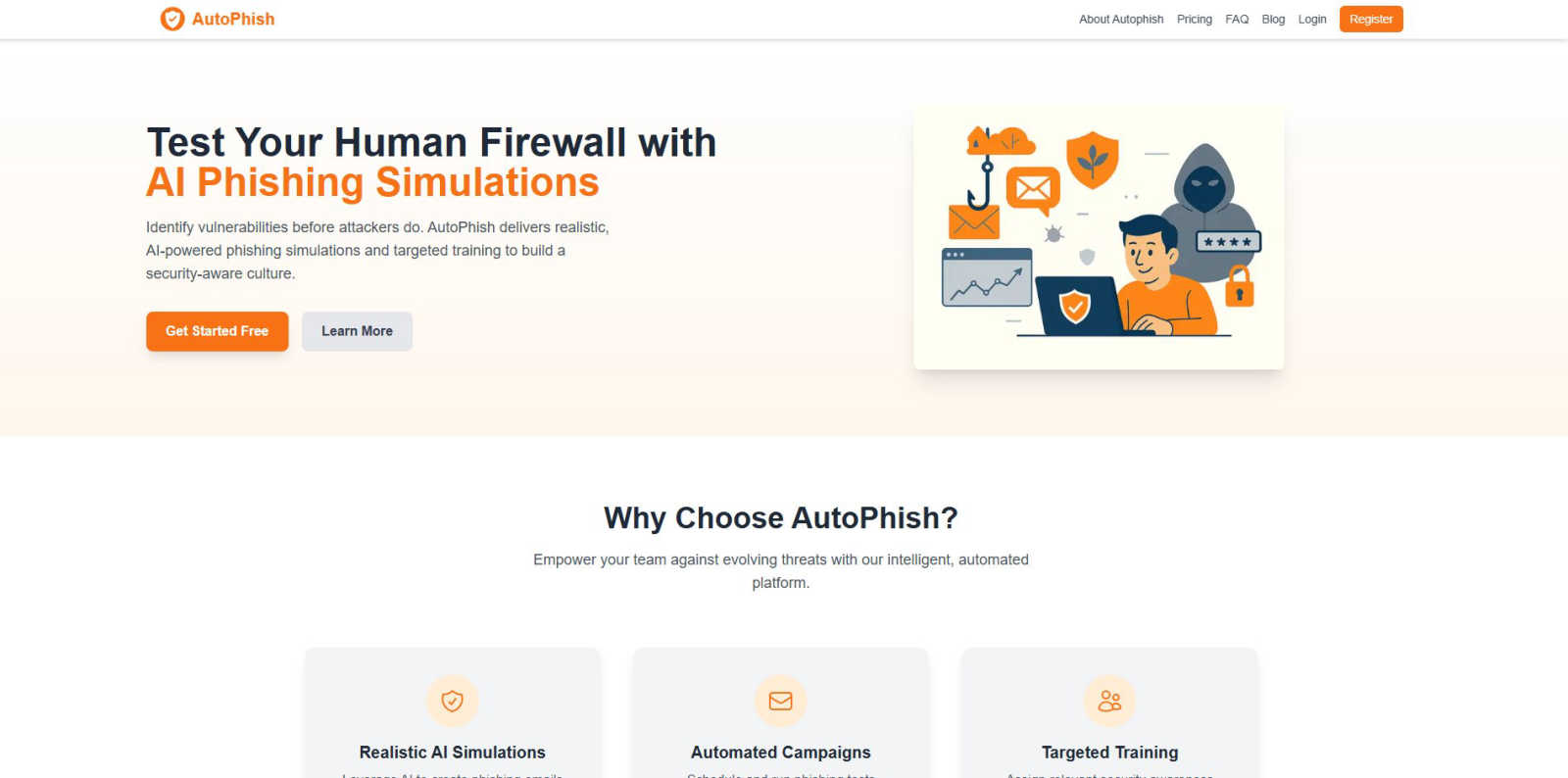
AutoPhish empowers teams with AI-driven phishing simulations and training to enhance security awareness and prevent.
Last updated: March 1, 2026
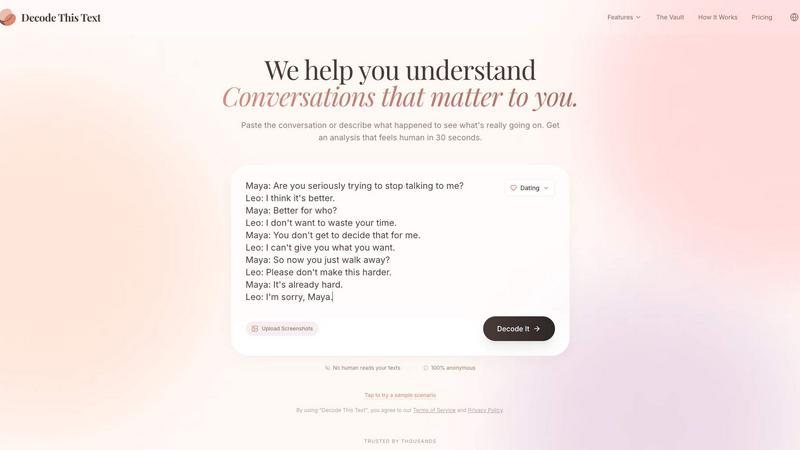
Decode This Text
Decode This Text gives you a wise, anonymous reality check on any confusing conversation in just 30 seconds.
Last updated: February 28, 2026
Visual Comparison
AutoPhish
Decode This Text
Feature Comparison
AutoPhish
Realistic AI Simulations
AutoPhish employs advanced AI technology to create phishing emails that closely mimic real-world attacks. These simulations are tailored to reflect industry-specific threats, providing employees with relevant experiences that enhance their ability to recognize and respond to actual phishing attempts.
Automated Campaigns
The platform allows users to schedule and execute phishing tests automatically, saving valuable time while ensuring that training remains consistent and up-to-date. This automation enables organizations to maintain a continuous security awareness program without additional administrative burdens.
Targeted Training
After each simulation, AutoPhish analyzes the results to identify vulnerable users and assigns relevant security awareness training based on their specific roles within the organization. This personalized approach ensures that employees receive the information they need to improve their security practices effectively.
Comprehensive Reporting
AutoPhish provides advanced reporting features that allow organizations to monitor the effectiveness of their training and simulations. Users can track progress over time, assess the overall security posture of their workforce, and make informed decisions based on the collected data.
Decode This Text
Screenshot Analysis
Gone are the days of manually transcribing lengthy chat histories. With this featured functionality, users can simply upload a photo of their text conversation. The tool seamlessly reads and analyzes the entire visual context, extracting every word, timestamp, and emoji. This streamlines the process immensely, allowing for a quick and effortless entry point to understanding complex or emotionally charged exchanges without the barrier of retyping.
Tone & Intent Deciphering
This feature acts as an emotional barometer for digital communication. It goes beyond dictionary definitions to measure the true emotional temperature of a message—assessing whether the sender is being cold, sarcastic, genuinely friendly, or passively aggressive. By quantifying elements like tone, effort, and intent, it provides an objective lens, helping users avoid the common pitfall of projecting their own anxieties or hopes onto ambiguous words.
Behavioral Pattern Detection
Human communication is rife with subtle, recurring cues that are easy to miss in the moment. This intelligent feature scans conversations for these critical behavioral patterns. It can highlight if someone only messages late at night, consistently avoids direct questions, or is gradually shortening their replies over time. Identifying these trends offers a strategic, big-picture view of the dynamics at play, revealing intentions that single messages might conceal.
AI-Generated Response Crafting
Paralysis over what to say next is a common experience. Decode This Text directly addresses this by generating contextually appropriate response options. After its analysis, it provides users with multiple tailored replies—often categorized as calm, direct, or firm. This empowers individuals to choose a response that aligns with their desired outcome, turning uncertainty into confident action and closing the communication loop effectively.
Use Cases
AutoPhish
Employee Onboarding
New employees can benefit significantly from AutoPhish by undergoing phishing simulations during their onboarding process. This prepares them for the types of threats they may encounter in their roles, fostering a security-conscious mindset from day one.
Ongoing Security Training
Organizations can use AutoPhish to conduct regular phishing simulations throughout the year. This ongoing training helps to keep security awareness fresh in employees’ minds, reducing the likelihood of successful phishing attacks.
Risk Assessment
AutoPhish allows organizations to periodically assess their employees' vulnerability to phishing attacks. By identifying weak points in knowledge and behavior, companies can tailor their training programs to address specific areas of concern.
Compliance and Regulation
For organizations subject to regulatory requirements regarding cybersecurity training, AutoPhish provides a means to demonstrate compliance. The platform's detailed reporting features allow companies to document their training efforts and show that they are actively working to mitigate phishing risks.
Decode This Text
Decoding Dating & Romantic Signals
Navigating the early stages of dating is fraught with mixed signals. Is "I'll let you know" a polite brush-off or a genuine statement from a busy person? When someone ghosts after a great date, what does it mean? This tool analyzes text exchanges to clarify interest levels, interpret silence, and explain confusing behaviors like breadcrumbing. It helps users understand the real subtext, saving them from overthinking and guiding them toward responses that protect their emotional well-being.
Interpreting Professional & Workplace Communication
Workplace communication often carries high stakes and hidden meanings. A terse one-word email from a boss, a vague "we'll keep your resume on file," or the challenge of saying "no" to a colleague without causing offense—all are ripe for misinterpretation. Decode This Text analyzes the tone and structure of professional messages, providing clarity on the sender's likely state of mind and suggesting diplomatically worded responses to navigate office politics with grace.
Understanding Friends & Family Dynamics
Group chats that go silent after your message, a friend's suddenly distant tone, or confusing family interactions can create social anxiety. This use case involves using the tool to parse conversations within personal circles. It helps determine if a comment was taken the wrong way, if someone is subtly upset, or if the silence is benign. The analysis fosters healthier relationships by providing an outside perspective on familiar dynamics, often more reliably than asking the same friends for advice repeatedly.
Analyzing Client & Business Correspondence
For freelancers, entrepreneurs, and sales professionals, clear client communication is crucial. Vague feedback, delayed responses, or ambiguous contract language can stall projects. Decode This Text can be used to analyze client emails or messages to discern their true level of satisfaction, urgency, or hesitation. Understanding the client's underlying tone and intent allows for more precise and effective follow-ups, ensuring projects stay on track and relationships remain positive.
Overview
About AutoPhish
AutoPhish is an innovative AI-powered platform designed to revolutionize cybersecurity defense by focusing on the human element, often referred to as the human firewall. Recognizing that employees can be both the strongest line of defense and a potential vulnerability, AutoPhish provides organizations of all sizes with hyper-realistic phishing simulations and targeted security awareness training. The platform operates on the principle that the most effective way to prepare employees for sophisticated cyber threats is through realistic testing in a controlled environment. By employing AI to craft deceptive but ethical phishing simulations tailored to various industries, AutoPhish helps organizations identify behavioral vulnerabilities among their workforce. Following these assessments, the platform seamlessly integrates role-specific training to bridge knowledge gaps. This proactive approach transforms security awareness from a mere compliance checkbox into a vital aspect of an organization’s culture, ultimately empowering employees to recognize and thwart phishing attempts before actual threats manifest, thereby safeguarding sensitive data and enhancing overall organizational resilience.
About Decode This Text
In the intricate dance of modern communication, where subtext often outweighs the words on the screen, Decode This Text emerges as a vital digital confidant. This innovative tool is designed to demystify the ambiguous messages that populate our inboxes and chat threads, transforming confusion into clarity. At its core, it is an AI-powered analysis engine that interprets the true meaning behind cryptic emails, vague texts, and confusing professional correspondence. By simply pasting a conversation, uploading a screenshot, or describing a scenario, users receive a comprehensive, human-feeling breakdown in about 30 seconds. This analysis delves into the underlying intentions, emotional tone, and even the unspoken patterns within the dialogue, providing actionable advice on how to respond. It serves a diverse audience—from anyone navigating the uncertainties of modern dating and friendships to professionals aiming to decode workplace nuance. Its primary value proposition is profound: to eliminate the anxiety of misinterpretation, enhance communication skills, and empower users to interact with confidence, all within a framework that is 100% anonymous and private.
Frequently Asked Questions
AutoPhish FAQ
How does AutoPhish simulate phishing attacks?
AutoPhish uses advanced AI algorithms to craft realistic phishing emails that mimic the tactics used by cybercriminals. These simulations are designed to challenge employees and help them recognize potential threats.
Can I customize the phishing simulations?
Yes, AutoPhish allows you to customize phishing simulations by choosing templates, target groups, and scheduling tests based on your organization's specific needs and industry-related threats.
What kind of training does AutoPhish provide?
AutoPhish offers targeted security awareness training that is role-specific. This ensures that employees receive relevant information tailored to their job functions, enhancing their understanding of cybersecurity best practices.
How does AutoPhish improve my organization's security posture?
By empowering employees to recognize phishing attempts and respond effectively, AutoPhish reduces the likelihood of successful attacks. The platform fosters a culture of security awareness, transforming employees into proactive defenders against cyber threats.
Decode This Text FAQ
How does Decode This Text protect my privacy?
Privacy is a foundational principle. The service is designed to be 100% anonymous. No human ever reads the texts, conversations, or screenshots you submit. All analysis is performed by secure AI algorithms. Furthermore, the company states that your data is not used to train their models, ensuring your personal conversations remain confidential and are not stored or reviewed by any person.
What kind of input does the tool accept?
The tool offers flexible input methods to suit your needs. You can directly paste the text of a conversation, write a descriptive summary of what happened, or use the featured Screenshot Analysis function to upload a photo of your chat. This allows you to analyze any digital interaction, whether it's a fresh text thread or a saved conversation from your camera roll.
Is the analysis really accurate if it's done by AI?
While not a substitute for human emotional intelligence, the AI is trained on vast datasets of communication patterns, linguistic cues, and social dynamics to provide highly insightful analysis. It excels at identifying consistent patterns, measuring tonal shifts, and offering probabilistic interpretations of intent based on common scenarios. Users report it feels like getting advice from a wise, objective third party, providing clarity that often cuts through personal bias.
Can it help me write a response?
Absolutely. One of the core features is the AI-generated response crafting. After analyzing the message, the tool provides you with several potential reply options tailored to the situation. These are typically framed with different strategic approaches (e.g., calm, direct, playful), giving you a starting point to communicate back with greater confidence and alignment with your goals.
Alternatives
AutoPhish Alternatives
AutoPhish is an innovative cybersecurity platform that specializes in training employees through realistic AI-driven phishing simulations. This tool is designed to strengthen the human firewall within organizations by providing targeted security awareness training that evolves with the tactics of cyber adversaries. As businesses increasingly recognize the importance of employee vigilance against phishing attacks, many users seek alternatives to AutoPhish to explore different pricing structures, feature sets, or platform compatibility that better fit their unique needs. When choosing an alternative to AutoPhish, users should consider several factors, including the realism of the phishing simulations offered, the comprehensiveness of the training modules, and the ease of campaign management. Additionally, organizations should evaluate the scalability of the solution to ensure it can accommodate their growth and evolving security challenges. A thorough understanding of these aspects will help users find a solution that aligns with their organizational goals and enhances their cybersecurity posture.
Decode This Text Alternatives
Decode This Text is a productivity tool designed to cut through communication ambiguity. It falls into the category of digital clarity and interpersonal management tools, helping users analyze confusing messages to understand tone, intent, and optimal responses quickly. People often seek alternatives for various practical reasons. Some may need a solution that fits a specific budget, while others require different feature sets, such as integration with particular platforms or more advanced analytical capabilities. The search can also stem from a desire for a different user experience or output style. When evaluating other options, consider your core needs. Key factors include the accuracy and depth of the analysis, the tool's speed, data privacy policies, and ease of use. The best choice will align with how you typically encounter confusing communications, whether in professional emails, personal texts, or social media interactions.

